OpenSSH with Two-Factor Authentication: Adding an Extra Layer of Security
Installing Google Authenticator
sudo apt-get install libpam-google-authenticator
Configuring Google Authenticator
google-authenticator
https://www.google.com/chart?chs=200x200&chld=M|0&cht=qr&chl=otpauth://totp/[email protected]%3Fsecret%3DWUGQECLUOFLAEAAZ
Your new secret key is: WUGQECLUOFLAEAAZ
Your verification code is 002879
Your emergency scratch codes are:
52979690
49230818
19888375
80196807
17714397
Do you want me to update your "~/.google_authenticator" file (y/n) y
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
By default, tokens are good for 30 seconds and in order to compensate for
possible time-skew between the client and the server, we allow an extra
token before and after the current time. If you experience problems with poor
time synchronization, you can increase the window from its default
size of 1:30min to about 4min. Do you want to do so (y/n) y
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting (y/n) y
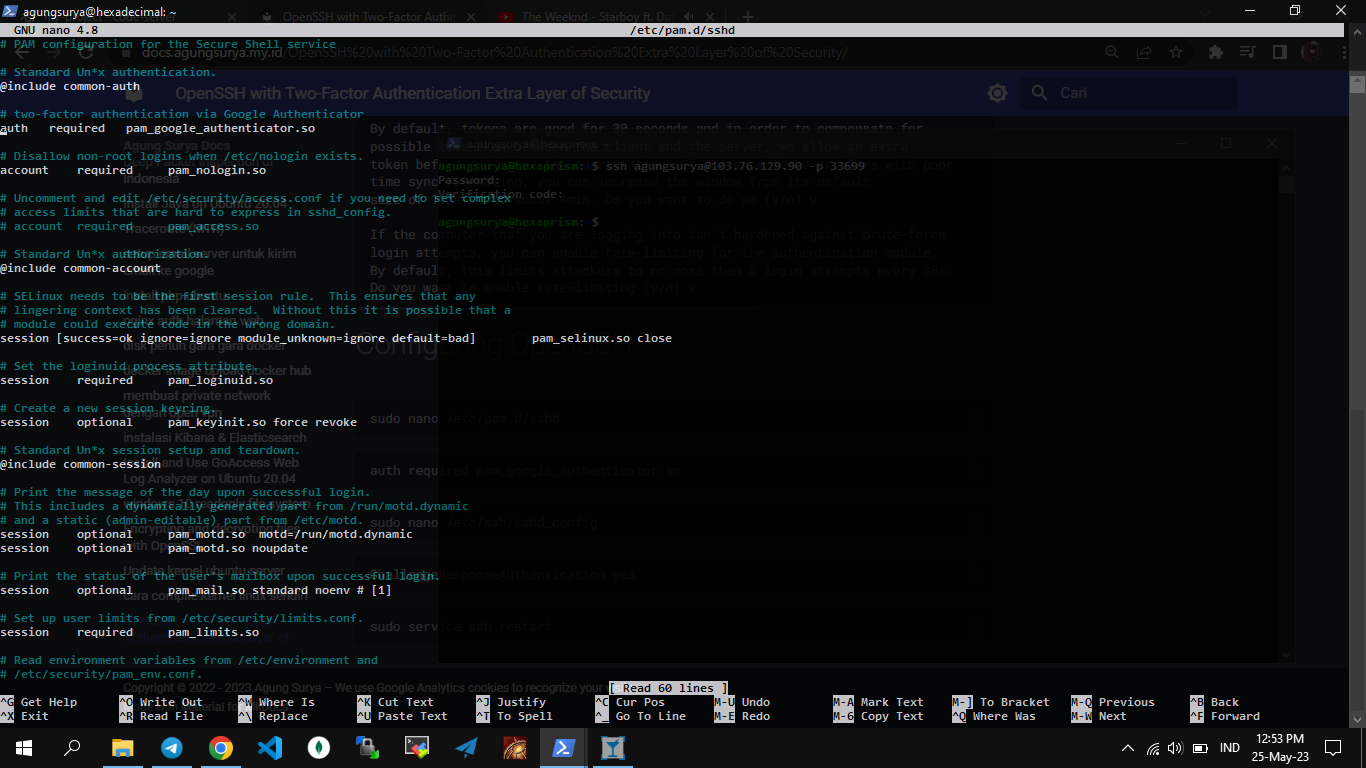
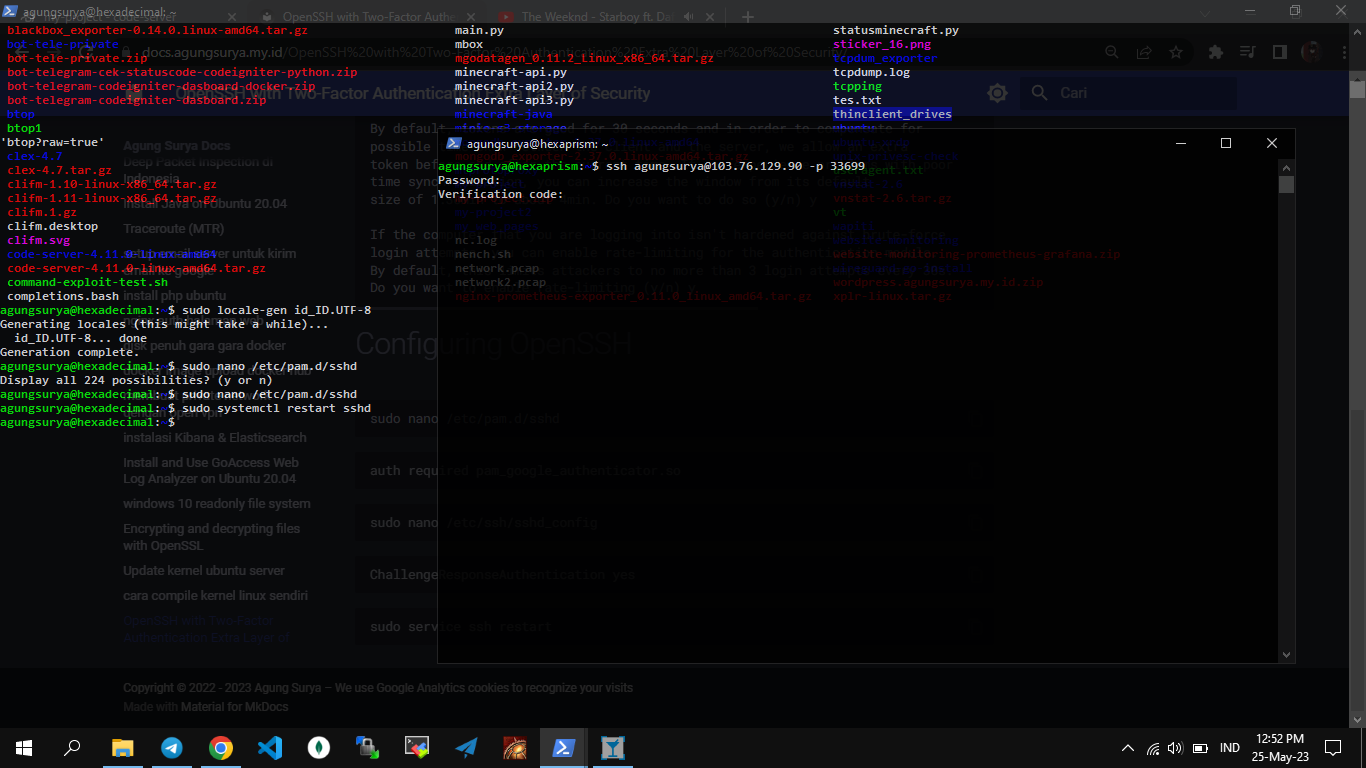
Configuring OpenSSH
sudo nano /etc/pam.d/sshd
auth required pam_google_authenticator.so
sudo nano /etc/ssh/sshd_config
ChallengeResponseAuthentication yes
sudo service ssh restart
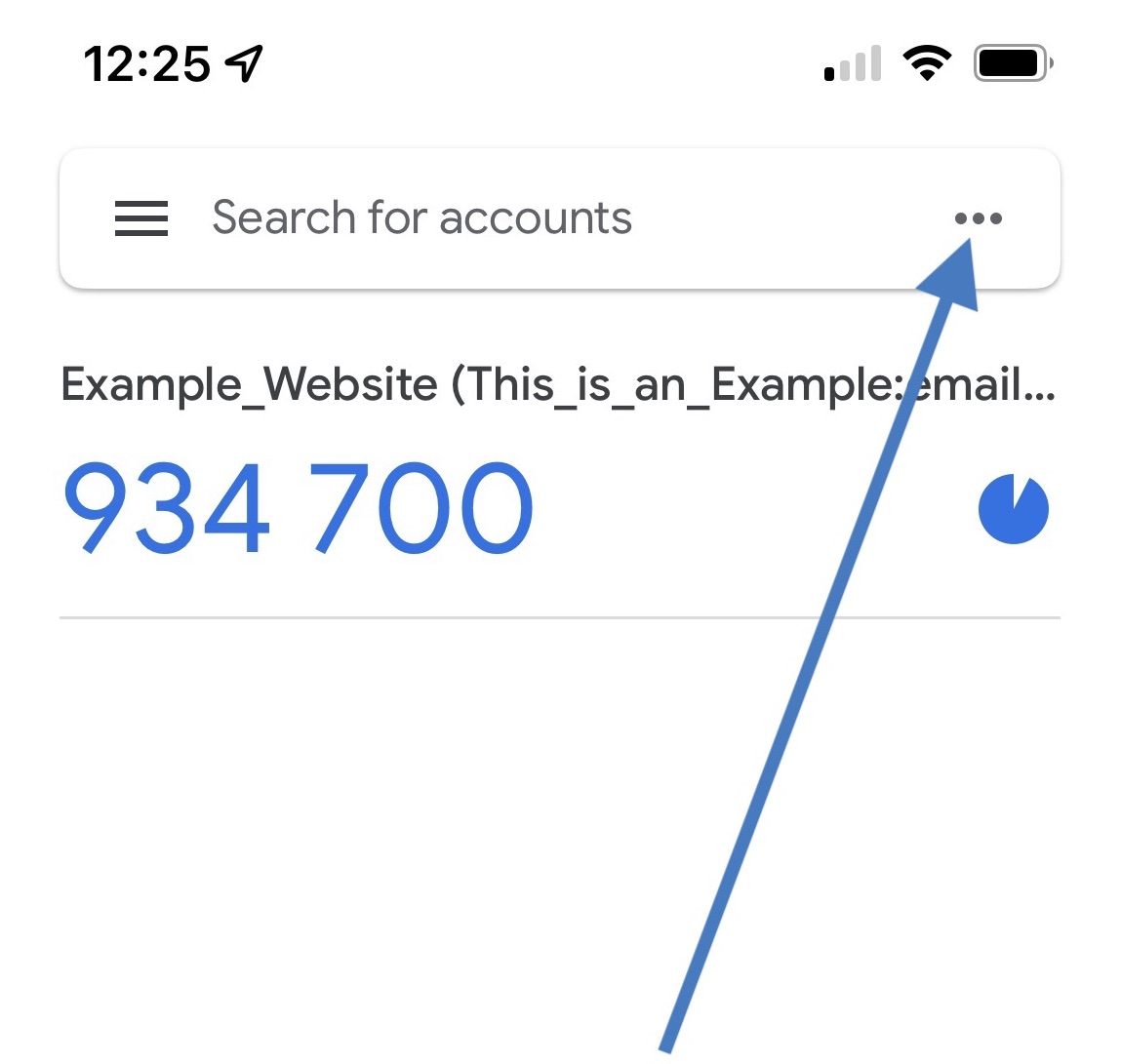
kode otp dari google authenticator